Brute force attacks are one of the most popular methods hackers use to gain access to a server or website. If you’re not properly protected, your sensitive information – and in some cases, your entire site – may be at risk.
Brute force attacks are one of the most popular methods hackers use to gain access to a server or website. If you’re not properly protected, your sensitive information – and in some cases, your entire site – may be at risk.
The good news is that there are a number of ways you can prevent these attacks. The simplest technique is to use complex passwords, but there are additional methods such as Two-Factor Authentication (2FA) and CAPTCHAs that you may also want to employ.
In this post, we’ll explain what are brute force attacks and how they work, and the damage they can cause to your site. Then we’ll offer advice for preventing this kind of attack, including by getting some expert help. Let’s jump right in!
An Introduction to Brute Force Attacks
In short, a brute force attack is when someone tries various passwords until they find the right one to break into an account. Typically, this is achieved by using a password-breaking program. Sophisticated hackers can use malicious bots to guess millions (or even trillions) of credentials per second.
For example, imagine that someone has created a two-digit password made up of numbers between one and nine. If you’re attempting to guess what it is, you can simply try every possible two-digit combination until you find the right one, out of the 100 unique possibilities.
However, most internet passwords are far more complex. They’re typically a minimum of eight characters long, and can include letters, numbers, and special characters. You might think the trillions of possible combinations make it impossible for hackers to guess a correct password, but it still happens quite often.
Even worse, if attackers do get into your site, they can steal valuable information, shut your site down, or use it as a base for more complex attacks. Additionally, they can infect your site with malicious scripts that you may not notice right away. Any of these situations could lead to your website’s downfall.

Types of Brute Force Attack
Simple Brute Force Attack
This are the guesswork attacks wherein the hacker tries to guess the credentials without the use of software tools to crack passwords. Simple brute force attacks are successful at times because the ones being attacked do not use best practices for passwords and choose passwords that are easily guessed.
Dictionary Attack
Dictionary attacks is one of the most common forms of brute force attack. They use a list of words in a dictionary to crack passwords. A dictionary attack will also try commonly used passwords unearthed through data breaches. It can also be used to find encryption keys to access encrypted data and decrypt it to access sensitive data.
Credential Stuffing
It is a cyberattack method in which hackers use lists of compromised user credentials to breach into a system or website. About 0.1% of breached credentials attempted on another service will result in a successful access.
Reverse Brute Force Attack
Reverse brute force attacks happen when hackers try to reverse engineer a protection process through utilizing a piece of data or leaked passwords. It is generally the reverse of a conventional brute force attack.
Hybrid Brute Force Attack
A hybrid attack add advanced tools to find out passwords that are a mix of words, numbers and characters. They usually mix dictionary and brute force attacks.
Password Spraying
This is a type of brute force attack where a hacker tries to guess a known user’s password using a list of common, easy-to-guess passwords such as “123456” or “password.” This occurs slowly overtime to remain undetected and is often an automated process.
Botnets
This are malwares that involves an inter-connected network of hacked computers that lead back to a centralized computer controlled by a cyber criminal. They use it to easily deploy cyberattacks within the network.
Brute Force Attack Tools
A hacker perform brute force attacks through an automated software that uses computing to systematically check password combinations until the correct one is identified. Using a brute force password cracking application is required in order to go through numerous combinations and possibilities that will decode login information and get the correct encryption key to use them to gain unauthorized access to systems.
Below are some of the tools that brute force attackers use:
- Aircrack-ng—this tool can be used on Windows, Linux, iOS, and Android.
- Hydra – quickly goes through a large number of password combinations. It can be used to attack more than 50 protocols and multiple operating systems and since it is an open platform; hackers and security community continue to develop new modules.
- John the Ripper— this application will try all possible combinations using a dictionary of possible passwords and runs on 15 different platforms.
- L0phtCrack—a tool for hacking Windows passwords.
- Hashcat—this tool can perform simple brute force, rule-based, and hybrid attacks and can be used on Windows, Linux, and Mac OS.
- DaveGrohl—an open-source tool for mainly cracking Mac OS.
- Ncrack—a tool for attacking network authentication.
5 Ways to Protect Yourself From Brute Force Attacks
Fortunately, there are several methods you can use to prevent brute-force attacks from happening. The following security best practices can help to protect your website and private data from hackers. Let’s take a look!
1. Use Longer and More Complex Passwords
A long and complex password is your first line of defense against an attack. The more sophisticated your passwords are, the more difficult they become to crack. This is why many systems now require passwords to be between eight and 16 characters long.
It’s also best if your passwords include upper and lowercase letters, numbers, and even special characters. To help you come up with secure combinations, some browsers offer to create strong passwords for your accounts:
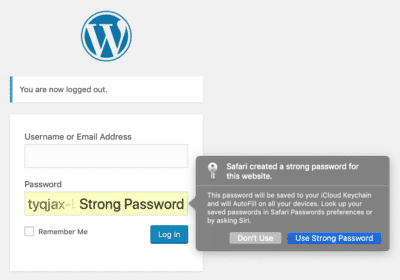
Similarly, WordPress includes a native password generator. Your users can create secure passwords for themselves, or you can generate passwords for them. Just log into your admin dashboard, navigate to Users, and select a profile. Then, scroll down to Account Management:
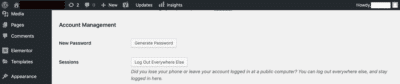
From there, click on Generate Password. This will create a password for the account that is very difficult for brute force attacks to crack. You can use this process on any user’s profile, as long as you have Administrator status.
2. Limit Login Attempts
Another powerful method you can use to combat brute force attacks is to limit login attempts. For example, if your website receives five failed attempts in a row, you can set it up to block further attempts from the offending IP address for a certain amount of time.
This slows down the brute force process considerably. The attacking program will have to wait before it can continue trying password combinations, and will often simply move on. In WordPress, you can use a plugin to implement this strategy. We recommend ShieldSecurity:

This tool is easy to set up and can be used to limit failed login attempts. Plus, it also includes other security features to help keep your site safe.
3. Consider Using CAPTCHAs
Completely Automated Public Turing tests to tell Computers and Humans Apart (CAPTCHAs) are tools you’ve likely seen on websites that have login functionality. CAPTCHAs present an additional barrier to users wishing to log into a system:
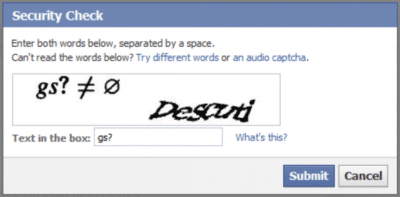
You can use CAPTCHAs to add a further layer of security to your website. They can be quite effective at preventing bots from executing automatic password attempts. To set one up on your WordPress website, simply install the Login No Captcha reCAPTCHA plugin:
This plugin adds a simple checkbox reCAPTCHA to your login, registration, and other vulnerable pages. This way, you can incorporate an additional layer of security without annoying your users.
4. Add an Extra Line of Defense With Two-Factor Authentication
Another effective way to prevent brute force attacks is to employ Two-Factor Authentication (2FA). This security measure requires an additional form of verification other than the user’s password – usually an email or a phone number – to log in.
Once again, ShieldSecurity can help you set up this feature:
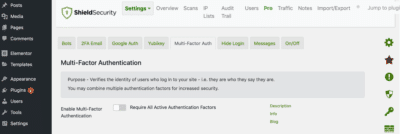
If you’re already using it to limit login attempts as we discussed above, you may also wish to enable 2FA, depending on the level of security you feel you need.
5. Hire WordPress Security Experts
Finally, you may wish to hire a service to help protect your site further. Many website maintenance plans – including ours – come with advanced security features, including some of the options we’ve already discussed:
These plans handle day-to-day security practices such as updates and malware scans for you. They’ll also keep you apprised of any newly-developed security measures. Simply put, this is the easiest way to manage security for your website.
At WP SitePlan, we offer an array of security services, including daily scans for malware, constant updates, and the removal of malicious viruses. If you’re looking for true peace of mind, our plans can help you cover your bases.
Conclusion
Brute force attacks are scary. Having sensitive information stolen can have a serious impact on your business, compromising your credibility. This is why taking measures to prevent such attacks is so important.
Five ways to protect your website from brute force attacks are:
- Use longer and more complex passwords.
- Limit login attempts.
- Consider using CAPTCHAs.
- Add an extra line of defense with 2FA.
- Hire security experts to keep your site safe.
Do you have any questions about brute force attacks and how to protect yourself from them? Contact us today!